https//www.racom.eu/eng/products/m/ripex/app/snmp/index.html
Table of Contents
List of Figures
- 2.1. MIB Browser example
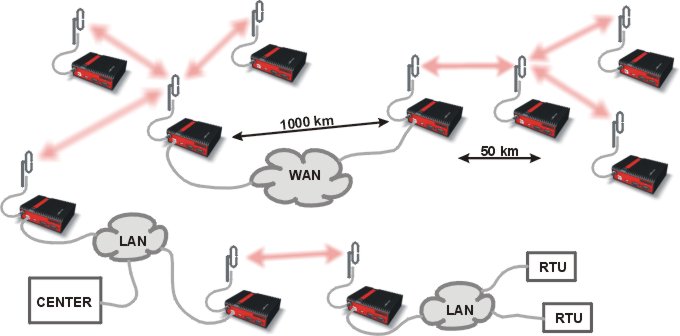
- 2.2. NMS communication with Slave stations
- 2.3. RipEX SNMP menu
- 2.4. RipEX Notification menu
- 2.5. RipEX Alarm management
- 3.1. RipEX images in Zabbix
- 3.2. New RipEX host
- 3.3. RipEX Host MACROs
- 3.4. Default RSS and DQ trap items
- 3.5. Edited DQ trap item details
- 3.6. Edited DQ trigger
- 3.7. Zabbix simple RipEX map
- 3.8. Host details in maps
- 3.9. Geographical map
- 3.10. Host GPS coordinates
- 3.11. Zabbix Geographical maps
- 3.12. Geographical map host details
- 3.13. URL link – maps
- 3.14. URL link – triggers
- 3.15. URL link – Inventory
- 3.16. Zabbix Media type – Email
- 3.17. User’s e-mail
- 3.18. Action and its conditions
- 3.19. Action Operations
- 3.20. Action Operations details
- 3.21. RipEX scripts in Zabbix
- 3.22. RSS sample script details
- 3.23. Host MACROs
- 3.24. RipEX scripts – map
- 3.25. RSS sample script output
- 3.26. RipEX Configuration backup script output
- 3.27. RACOM Branding
- 3.28. RACOM Branding login page