To access our SNMP values, any Network Management System (NMS) can be used. However, we recommend using the ZABBIX open source monitoring system. It can be downloaded at http://www.zabbix.com/download.php.
Zabbix features are explained here – https://www.zabbix.com/features.
If you have chosen the Zabbix software, please read the following pages where we offer a basic Starting Guide to RAy3 and Zabbix co-working.
Whatever your choice of NMS, these sections may provide general hints and tips anyway.
| Note | |
|---|---|
The following guide was tested with Zabbix LTS version 6.0. If you have older Zabbix releases, check the RAy3 Archive download section for previous versions of this application note. |
Take the opportunity to remotely access and test a live Zabbix demo. See the credentials within the text on the given link.
Follow the Zabbix documentation, download packages from https://www.zabbix.com/download and install Zabbix 6.0 LTS. We suggest using Debian11 (or newer) OS, MySQL database and Apache web server, because of our good experience and knowledge. If using different solution, our help can be limited.
| Note | |
|---|---|
With previous Zabbix versions, we suggested using CentOS7 and CentOS8, but due to changes in distributing these operating systems, Debian OS seems to be much more appropriate. |
Zabbix also offers paid support – see all the possible support tiers at https://www.zabbix.com/support.
Once Zabbix 6.0 LTS is installed, multiple additional installation steps are required so that you can monitor and maintain your RAY3 (and any other RACOM products) network(s). Required steps are explained later within this application note.
We also offer Zabbix 6.0 LTS as a virtual, ready-to-be-used, image. It is called “RACOM Zabbix Appliance” or in short “RZA6”. Within this .ova image, functionality for all RACOM products is already installed and ready to be used. Contact RACOM support to obtain this virtual machine and stay in touch with us for more details.
You can run this RZA6 as a virtual machine, e.g., within your VMware or VirtualBox environment (or any similar one).
Once you finish basic Zabbix 6.0 LTS installation following the Zabbix documentation, you can and should check this part for more details about required steps for RACOM products Zabbix support. The order of explained steps is not so important usually.
| Note | |
|---|---|
If there is any particular Linux command, it is based on Debian11 OS. |
We suggest various applications for future usage:
traceroute
nmap
zabbix-sender
sshpass
All the commands can be installed from the command line with:
# apt-get install traceroute nmap zabbix-sender sshpass
If you need, you can implement sending PDF reports automatically. The installation and functionality can vary from version to version so we do not describe step-by-step procedure here. Use Zabbix documentation for more details.
For RACOM products, multiple steps are required. Upload all the MIBs from respective devices (RAy3 in our case) to /usr/share/snmp/mibs/ directory. For a proper functionality, add them to SNMP configuration file /etc/snmp/snmp.conf. E.g.:
mibs +/usr/share/snmp/mibs/MG-MIB.txt mibs +/usr/share/snmp/mibs/RacomRay3.mib mibs +/usr/share/snmp/mibs/RacomRay2.mib mibs +/usr/share/snmp/mibs/RACOM-RipEX-1.0.4.0.mib mibs +/usr/share/snmp/mibs/SNMPv2-TC.txt mibs +/usr/share/snmp/mibs/RACOM-RA2-MIB
Download RAy3 Zabbix 6.0 template from RACOM website. Unzip the file and import zbx_export_ray3.yaml into your Zabbix instance in Configuration -> Templates menu via web interface.
Approximately 90 enabled items are included in RAy3 templates. Most items are implemented by RACOM, but there are also items from the well-known MIB files IF-MIB and RMON.
| Note | |
|---|---|
Some items are disabled by default. |
The provided templates have predefined update intervals and for how many days each item keeps its history and trend values. All of these parameters define the requirements for the Zabbix server performance and the database size.
Update interval [seconds] | Refresh the item every N seconds. |
Keep history [days] | Number of days to keep detailed history in the database. Older data will be removed by the Housekeeper. |
Keep trends [days] | Keep aggregated (hourly min, max, avg, count) detailed history for N days in the database. Older data will be removed by the Housekeeper. Note that trends are only stored for numerical items. |
Based on these parameters, items are divided into four groups:
Update interval = 1 day (86400 seconds), History = 30 days, Trends = 400 days
Update interval = 1 hour (3600 seconds), History = 30 days, Trends = 200 days
Update interval = 5 minutes (300 seconds), History = 60 days, Trends = 400 days
Update interval = 1 minute (60 seconds), History = 400 days, Trends = 400 days
Group 4 consists of the most useful values to watch:
Input “Ethernet1” data port throughput in bps
Output “Ethernet1” data port throughput in bps
Current net bitrate in bps
Current RF Power in dBm
Receive RSS indicator in dBm
Receive MSE indicator in dB
From our experience, all these values are important to watch and to have them updated each 60 seconds. It is also useful to be able to display these values in detail even if they are one-year-old.
If you need to have even more accurate values, you can decrease the update interval. The smallest useful value for the throughput items is 10 seconds. Reading RSS or SNR can be done every second, because its value is always the current one.
| Important | |
|---|---|
We calculated that with the predefined RAy3 template (enabled values only), you approximately need about 0.75 GB of data for one RAy3 link (two units). Have this in mind when considering the database size. It can be increased a lot in case of many traps being sent from the RAy3 units |
The link reliability, link uptime, downtime or BER can be read because of our own OIDs. These values are updated every 5 minutes by default.
Watching the number of CRC errors can detect faulty cables and the number of dropped packets can warn you about high Ethernet traffic (bursts) so RAy3 drops some of them.
By default, the templates automatically populate the Inventory of individual hosts (serial number, unit type, MAC address, …). If you enable Inventory of your RAy3 hosts (in the host configuration menu), you’ll be able to see those values within the unit’s Inventory without any additional steps or without configuring them manually.
| Note | |
|---|---|
You can define the default Inventory mode in the Administration – Others menu. |
It is also recommended to utilize SNMP BULK requests which significantly reduce amount of data being exchanged between RAy3 and NMS, because it is possible to query multiple OIDs within a single packet, as well as reply to such multiple requests within just one SNMP reply packet.
| Note | |
|---|---|
There are many Network Management Systems available on the market. Whichever you choose, keep in mind the described limitations. E.g., never use NMS, which can download only the entire remote device MIB and not single OIDs |
SNMP Traps
Other important steps are for SNMP traps. Once the trap is received, it is handled by our script and for its proper functionality, the OID cannot be translated to text. Edit the snmptrapd:
# systemctl edit snmptrapd.service --force –full
Change the ExecStart variable:
ExecStart=/usr/sbin/snmptrapd -Lsd -f -p /run/snmptrapd.pid -On
The whole file should be:
# cat /etc/systemd/system/snmptrapd.service [Unit] Description=Simple Network Management Protocol (SNMP) Trap Daemon. After=network.target ConditionPathExists=/etc/snmp/snmptrapd.conf [Service] Type=simple ExecStart=/usr/sbin/snmptrapd -Lsd -f -p /run/snmptrapd.pid -On ExecReload=/bin/kill -HUP $MAINPID [Install]
For a proper functionality of RAy3 SNMPv2c traps, multiple additional steps are required. Also keep in mind that you could configure RAy3 traps different way (e.g., via SNMPTT) – here is just one approach described.
If not yet installed, install ‘snmptrapd’ daemon and enable it to be run automatically.
Within the downloaded .zip templates from RACOM website, snmptrap.sh script is included. Copy the script into /usr/lib/zabbix/externalscripts/ directory and change the file privileges and make it executable.
# chown zabbix:zabbix /usr/lib/zabbix/externalscripts/snmptrap.sh # chmod +x /usr/lib/zabbix/externalscripts/snmptrap.sh
| Note | |
|---|---|
Your ‘zabbix’ user should be enabled. It should have a HOME directory set to /var/lib/zabbix/ and this user should be able to run the shell. E.g., this command can be helpful: |
# usermod --shell /bin/bash zabbix
Check your ‘zabbix_sender’ path and if required, change it within the provided snmptrap.sh script accordingly.
# which zabbix_sender /usr/bin/zabbix_sender
So, the script has this line inside:
ZABBIX_SENDER="/usr/bin/zabbix_sender";
The script parses the output of each received SNMP trap, selects the appropriate host and declares an associative array containing trap descriptions. Eventually, it sends the whole message to your Zabbix server.
The default path to a LOG file from snmptrap.sh script is /var/log/snmptrap/snmptrap.log. Create the directory and a file manually, if not yet created.
Another required step from the command line is to edit /etc/zabbix/zabbix_server.conf file. Find the appropriate lines and edit them to:
SNMPTrapperFile=/var/log/snmptrap/snmptrap.log StartSNMPTrapper=1
Zabbix, and especially your snmptrapd must know how to authenticate against the received traps/informs. If it is SNMPv2, it is quite easy – you just need to allow particular community strings and also explicitly say that our snmptrap.sh must be executed upon a received trap/inform. Do this via /etc/snmp/snmptrapd.conf file. Example of such file:
authCommunity log,execute public authCommunity log,execute mwl-snmp authCommunity log,execute racom-snmp traphandle default /bin/bash /usr/lib/zabbix/externalscripts/snmptrap.sh
| Note | |
|---|---|
There is third trap state on the RAy3 WEB interface – “acknowledged”. This is not recognized automatically within the Zabbix frontend, but you can acknowledge the trap in Zabbix separately from the Dashboard menu. |
Since RAy3 FW 1.0.14.0, the SNMP non-table items OIDs are defined in accordance with the RFC (ending ‘.0’) – to improve SolarWinds compatibility. Keep this in mind when upgrading RAy3 firmware. Firmwares < 1.0.14.0. are able to reply to SNMP queries with OIDs ending with .0, but the reply does not contain .0 in its OID. This works fine (for example) with Zabbix NMS, but (for example) SolarWinds does not accept such replies.
Since RAy3 FW 1.0.16.0, the SNMP product OID of RAy3 changed from ‘1’ to ‘4’. The old template will NOT work with new RAy3 firmware. See the procedure below.
Suggested way of updating the RAy3 template is very straight-forward. Download the latest template from our RAy3 Firmware download site. The name of the template is “RAy3 Template”. There are two possible procedures and situations.
All RAy3 units in your NMS already have firmware >= 1.0.16.0. Rename your current RAy3 template to “RAy3 Template” and Import the new one with the same name. This will replace the older template.
You operate both RAy3 links with newer and older firmware. In such a case, you need two different templates. Make sure that your current template in Zabbix has a different name than “RAy3 Template”, e.g. “RAy3 old firmware Template”. Then, import the new template.
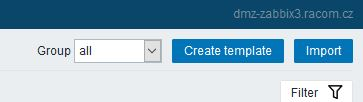
Mark hosts with new firmware (>= 1.0.16.0) and use “Mass update” button.
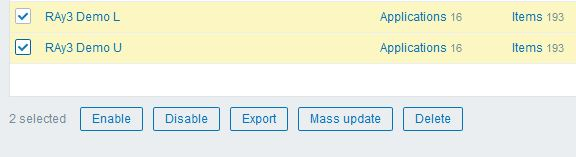
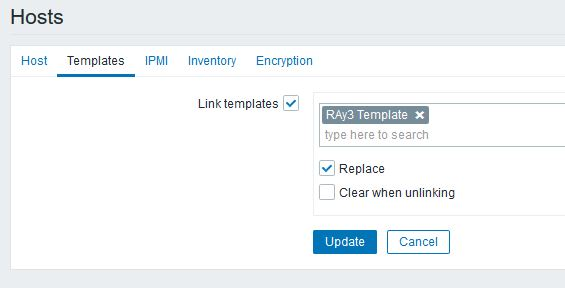
Select the “Templates” submenu and select a new template. Check the “replace” box and apply the changes.
In both situations, the history values should still be available and new values will be queried successfully.
If you have any issues updating RAy3 firmware and/or Zabbix templates, contact RACOM technical support group via support@racom.eu.
| Note | |
|---|---|
If you use template utilizing Item’s KEYs of non-table items with ‘.0′ at the end, you need to check the “Clear when unlinking” box once replacing hosts’ template, because you would double the Items of each host. Unfortunately, you lose your historical data. You could manually edit all Item keys with trailing .0 manually in Zabbix GUI. |
Hosts can be displayed in graphs. For such a purpose, we created multiple RAy3 images of different size and with different borders (e.g., red border in case the unit is in a problem state). These images are included in the mentioned .zip file with RAy3 template. Import them one by one in Administration – General – Images menu, or via directly via MySQL.
Now, Zabbix should be ready for monitoring RAy3 network. This chapter gives you a brief procedure to get started, but feel free to utilize different approach.
First, we suggest to create a Host – probably RAy3 unit directly accessible via Ethernet from Zabbix. Go to the Configuration – Hosts menu and click on the “Create host” button on top right corner.
Always put the IP address of the unit to the “Host name” field so the SNMP traps work (the script works with IP addresses). The “Visible name” can be set to any required value.
Select the “RAy3 Template” so that the unit is preconfigured with all RAy3 supported Items. Create a new, or add it to an existing one, RAy3 group. You can name it as required – e.g., based on RAy3 network location or particular customer company name. Set the SNMP Interface:
IP address
Port (usually UDP/161)
SNMP version 2
Set the community string to MACRO {$SNMP_COMMUNITY}
Now, check and change MACROs in “Macros” tab
HOST_SSHKEY and HOST_SSHPORT macros are used for RAy3 scripts
You can either change the values in Template so it is the same in all your RAy3 units, or you can set it per Host.
Check the “Use bulk requests” option because it optimizes data traffic being sent
Verify the Inventory tab – it should be set to “Automatic” so some of the values are automatically filled by SNMP queries. Click on the “Add” button – a new Host is created.
But the host is not monitored yet, because all the Items and Discoveries are disabled by default.
Only monitor the values which you really need and with reasonable update times.
Go to the Host’s Items and enable required Items, you can also edit the SNMP query intervals and other parameters.
If you want Traps to be working, you need to enable particular traps with App tag equal to TRAPS and enable Triggers accordingly (i.e., if you enable “TX Lost value out of range” Item, you also need to enable a Trigger for this Item).
You can check the data in the Monitoring – Latest data menu. Filter the values are required. All numeric values can be depicted in graphs. String values have their own history.
Other units can be easily added by a “Clone” button from this Host configuration. Just change appropriate IP addresses and ports. Divide them into groups (e.g., geographically). Choose wisely the monitored values and enabled discovery rules.
This application note cannot target all possible information about Zabbix and its usage. Check Zabbix documentation and Google forums for general help and guides. The following section provides several hints and tips for quicker and easier RAy3 network monitoring. Information provided might not be fully explained or might be different in any other Zabbix version other than 6.0 LTS.
Having a map is handy way for a network overview. On a single map, or multiple maps (even hierarchical) you may see all RAy3 units (and any other devices) and their status overview. There can be a plain/empty background, or e.g., some picture of a map (static).
On the map above, we can see two RAy3 units with a displayed name and current RSS, MSE and temperature. If the unit has no Problem, an “OK” message is displayed and the Host borders are in green color. We also depict a radio link between these units and its throughput values.
Host details:
Label is set as follows:
RAy3 {HOSTNAME} – RACOM
RSS= {?last(//rss)}
MSE= {?last(//mse)}
Temp= {?last(//temperatureModem)}Select a particular host and you can change icons for various situations.
Example of the link Label:
{?last(/10.10.0.188/netBitrate)}
{?last(/10.10.0.189/netBitrate)}Even the link color can change in time – for example lower throughput than 20 Mbps. You can create your own Trigger monitoring throughput values.
New feature from 6.0 LTS Zabbix version are Geographical maps. If you add GPS coordinates to your RAy3 hosts, you can display them on geographical maps.
First, you need to add GPS coordinates in the Host Inventory.
Another step is to enable and configure Geographical graphs. Go to Administration – General – Geographical maps menu. Set the required map source/provider. There is a list of default supported map sources, but you can also add “other”. Here is the example for Czech mapy.cz map source.
Tile URL: https://mapserver.mapy.cz/turist-m/{z}-{x}-{y}
Attribution: <a href=”https://napoveda.seznam.cz/cz/mapy/mapy-licencni-podminky/licencni-podminky-mapovych-podkladu/%22%3E%C2%A9 Seznam.cz, a.s.</a>
Max zoom level: 18
The last step is to add Geographical map to your Dashboard. Edit the dashboard and add “Geomap” widget. Select its name, host group(s) and host(s). Save the changes.
Within the map, you can use a “zoom” feature. You can either see multiple hosts within one icon, or one icon is one host (it is zoomed enough). You can then be forwarded into particular menus etc. Color of the Icons can be changed upon Host status. Read more in Zabbix documentation.
Units’ GUI can be accessed from Zabbix web interface from multiple menus.
A typical one is from simple maps. Configure the URL within the Host on the map and once you click on the Host in this map afterwards, you can be forwarded there. Keep in mind it is not possible from geographical maps.
Another way is a link from Triggers so that if a Problem occurs, you can quickly go to the required web interface.
The third option is to use Inventory for configuring URL. For every Host, you can enable the Inventory (serial number, OS, host type, …). Within many Inventory options, the URL can be defined.
Another useful feature is generating scheduled reports. You need to configure Scheduled reports in general. Once you have it, go to the Report – Scheduled reports menu and create a new one. Basically, Zabbix can send multiple users in regular intervals its Dashboard(s) as PDF.
More information e.g., see Zabbix website.
In case of any issue within your network, e.g., drop in the signal quality, or the unit being unreachable, Zabbix can automatically send an e-mail to predefined e-mail addresses. See the following example for your reference, but customize it to suit your needs.
The e-mail can be set in the Administration – Media Types menu. Edit the E-mail type corresponding to your server settings. In our example, we use our own SMTP server reachable from Zabbix server. No special security or password is required. You should be able to use any SMTP server.
The e-mails are sent to the users’ e-mail addresses. Go to the Administration – Users menu and configure the required e-mail addresses within the user’s details (Media).
You define the time when the e-mail will be sent (e.g., do not send it over the night) and the severity of the issue (e.g., send me the e-mail just in case of a critical issue).
The last step is to configure the action – configure which issue causes the e-mail to be sent. Go to the Configuration – Actions – Trigger actions menu and create a new Action. Set a Name of the Action and its Conditions – trigger severities and host group are used within the screenshot below.
Within the Operations tab, define one or multiple operations. In the example, once the Problem occurs, Zabbix sends an email. It sends such email every other day until the problem is fixed.
We also send a Recovery email to all involved recipients.
Usually, you will use the MACROs for the e-mail body/subject. In this example, the Subject of the email will consist of the host’s Name, Trigger status (Problem or OK) and Event Name. Within the body of the message, there can be additional information such as the Trigger Severity, URL and the Issue details.
By default, there are no ready-to-be-used actions in Zabbix such as configuration backup or firmware upgrade. The Zabbix NMS is a general system which requires special features to be implemented by RACOM or by the user himself.
We provide the user with a guide how to use and define these special features and within the RAy3 template, we already prepared several examples:
Configuration backup
Displaying the current Firmware version
Firmware upgrade
| Note | |
|---|---|
If you have troubles running those scripts or making your own, contact RACOM technical support on support@racom.eu. |
The whole implementation can be quite time consuming, but once you successfully run the first script, the others are very similar and its implementation is straightforward.
Within the Template, there are three scripts. As you realize, having the configuration backup files can be crucial if replacing the unit. There is nothing easier than just uploading the configuration file into a brand new RAy3 unit.
Before creating and running the first scripts, you need to prepare the Zabbix server (and the Linux operating system). In this example, we configure the Debian11 OS with Zabbix 6.0 LTS installed via packaging system.
The following steps can be done in different order, but following this order is absolutely fine.
By default, the zabbix_server configuration file is located in the /etc/zabbix/zabbix_server.conf file. Find the line with “SSHKeyLocation” parameter and define it with this value:
SSHKeyLocation=/var/lib/zabbix/.ssh
This is the location of the private SSH key which will be used to access the RAy3 units. Restart the Zabbix server afterwards.
systemctl restart zabbix-server
The scripts must be uploaded manually to a correct directory. The default directory is /usr/lib/zabbix/externalscripts/. Copy the script files from the ZIP Template file to this directory. The target state should look similar to this output:
ls -l /usr/lib/zabbix/externalscripts/ -rwxr-xr-x 1 zabbix zabbix 649 Mar 9 16:58 ray_cli_cnf_backup_get.sh -rwxr-xr-x 1 zabbix zabbix 137 Mar 9 13:59 ray_cli_fw_show.sh -rwxr-xr-x 1 zabbix zabbix 3202 Mar 15 08:40 ray_cli_fw_upgrade.sh -rw-r--r-- 1 zabbix zabbix 9612 May 25 09:31 script-log.txt -rwxr-xr-x 1 zabbix zabbix 39262 May 26 08:44 snmptrap.sh
There are three executable scripts via the Zabbix web interface (starting with “ray_”). The LOG output of those scripts is in script-log.txt file. There is also the snmptrap.sh file which you should have there for the SNMP TRAP functionality.
Make sure that the files have the zabbix user/group and are executable.
# chown zabbix:zabbix /usr/lib/zabbix/externalscripts/* # chmod +x /usr/lib/zabbix/externalscripts/*.sh
The Zabbix user cannot login to the bash by default. We need to enable it as follows (if not already done in RZA6).
usermod --shell /bin/bash zabbix
If not already created, create the HOME directory for the Zabbix user.
usermod -m -d /var/lib/zabbix zabbix chown zabbix:zabbix /var/lib/zabbix chmod 755 /var/lib/zabbix
Create the directories for the saved configuration and firmware files and change the access rights.
mkdir /var/lib/zabbix/configuration-backup mkdir /var/lib/zabbix/configuration-backup/ray mkdir /var/lib/zabbix/firmware mkdir /var/lib/zabbix/firmware/ray3 chown -R zabbix:zabbix /var/lib/zabbix/
The directory for the SSH key should now be located in /var/lib/zabbix/.ssh directory. Change the current directory to this one and login as zabbix.
su zabbix
A new prompt appears. We need to upload the SSH keys into every unit we want to control. You can either have you own RSA/DSA key or you can create a new one following this example. Run
ssh-keygen -t rsa
Follow the guide of the ssh-keygen application and leave the passphrase empty. To copy our RSA key into RAy3 units, copy the public part of the key and run the following command:
ssh admin@192.168.132.200
Just replace 192.168.132.200 with the correct RAy3 IP address. The prompt will ask for the admin password, fill it in and click Enter. Now, you should be logged in RAy3 CLI. Run the following command:
vi .ssh/authorized_keys
| Note | |
|---|---|
Browse the Internet for how to use ‘vi’ text editor if you are in trouble. |
Insert (paste) your public part of the key to a new line. Save the changes and close the file. Logout and check, if you can access the unit without a password.
ssh -i rsa admin@192.168.132.200
We completed all Linux tasks, but we still need to edit Zabbix web interface.
Scripts must be manually created in the Zabbix Administration – Scripts menu. See the example below and create Zabbix scripts for RAy3 units.
If you open one of them, you can modify them as required. If you do not have any, you need to create them from scratch.
Configuration backup – the script creates a configuration backup file in /var/lib/zabbix/configuration-backup/ray/ directory. The name is taken from RAy3 S/N and Ethernet IP.
Name: RAy3 Configuration backup
Scope: Manual host action
Menu path: RAy3
Type: Script
Execute on: Zabbix server
Commands:
/usr/lib/zabbix/externalscripts/ray_cli_cnf_backup_get.sh {HOST.CONN} {$HOST_SSHKEY} {$HOST_SSHPORT} 2>>/usr/lib/zabbix/externalscripts/script-log.txt
Set other parameters to suit your needs.
Displaying firmware version – the script reads a current FW version installed in RAy3 unit.
All is the same, except the “Commands” parameter:
/usr/lib/zabbix/externalscripts/ray_cli_fw_show.sh {HOST.CONN} {$HOST_SSHKEY} {$HOST_SSHPORT} 2>>/usr/lib/zabbix/externalscripts/script-log.txt
Upgrading firmware version – the script uploads a firmware file and a special CLI script into local RAy3 unit which is then executed and FW of both units within the link are upgraded. The script command is:
/usr/lib/zabbix/externalscripts/ray_cli_fw_upgrade.sh {HOST.CONN} {$HOST_SSHKEY} {$HOST_SSHPORT} “/var/lib/zabbix/firmware/ray3/ray3-fw-2.0.3.0.cpio” “2.0.3.0” 2>>/usr/lib/zabbix/externalscripts/script-log.txt
The parameters are MACROs which should be enabled by default due to our Template. Each RAy3 unit uses the SSH port 22 and the SSH key saved in /var/lib/zabbix/.ssh/rsa file by default. If you need to modify any of these parameters, go to the Configuration – Hosts menu and edit the particular Host’s MACROs.
The easiest script displays the FW version.
Another script is the Configuration backup. The expected output should display a full path to the stored file.
The last script should be first tested and verified in RAy3 units/links which are e.g., on your desk so that you double-check a correct behaviour.
Zabbix 6.0 LTS offers you to use your own company’s branding instead of Zabbix ones, or RACOM logos in case of using RZA6.
General and brief procedure is described here:
https://www.zabbix.com/documentation/current/en/manual/web_interface/rebranding
For the RZA6, we created a file /usr/share/zabbix/local/conf/brand.conf.php with this content:
<?php return [ 'BRAND_LOGO' => 'racom/racom_logo.png', 'BRAND_LOGO_SIDEBAR' => 'racom/racom_logo.png', 'BRAND_LOGO_SIDEBAR_COMPACT' => 'racom/racom_logo_compact.png', #'BRAND_HELP_URL' => 'https://www.racom.eu/ APP NOTE LINK ' ];
Logos were scaled to 140×20 and 20×13 (compact one). The logos are placed in /usr/share/zabbix/racom/ directory. After these changes, the Login screen can look like:
If you need any additional help or information, do not hesitate to contact support@racom.eu. We are ready and happy to help you.
We do recommend using our RZA6 solution. If not in your real network, then as a start for getting familiar with RAy3 SNMP and Zabbix NMS, because RZA6 has many configuration steps pre-configured and done.